A Practical Guide to Security Risk Assessment
- Marketing Team

- Dec 29, 2025
- 16 min read
Updated: Dec 29, 2025
Let's be honest, most security risk assessments feel like a chore—just another box to check for compliance. But what if you could reframe that entire process? A modern security risk assessment is one of your organization's greatest strategic advantages, turning a tedious necessity into a proactive defense system that protects what actually matters.
This is your chance to turn a mandatory task into a powerful tool for building a resilient and trustworthy organization.
Rethinking Your Security Risk Assessment
Forget the old playbook of dusty binders and once-a-year check-ins. A truly effective security risk assessment is a living, breathing process. It has to move beyond just scanning for technical vulnerabilities to address the far more nuanced world of human risk.
It’s not just about firewalls and software patches; it's about understanding the complex interplay between your people, your processes, and your technology.
The goal is to flip the script from a reactive stance—scrambling after a breach—to a proactive one. This means identifying the subtle, early signals of risk before they escalate into full-blown crises. It requires a holistic view that acknowledges threats can come from anywhere, both outside and inside your organization.

Beyond Technical Scans to Human Insights
Traditional assessments are great at finding technical gaps, but they almost always miss the biggest variable: people. A modern approach brings the human element into focus, looking at the behavioral indicators and procedural weaknesses that create opportunities for risk.
This isn't about invasive surveillance. It's about using ethical, AI-driven insights that preserve employee dignity and privacy while spotting genuine threats.
Instead of just asking, "Is our network secure?", a forward-thinking assessment also asks:
Are there unidentified conflicts of interest that could compromise decision-making?
Do our internal processes accidentally create easy opportunities for fraud or data leakage?
Are employees showing behavioral signs of pressure that might lead to accidental or intentional misconduct?
This comprehensive perspective helps you spot preventive risks that automated tools alone will never see.
A successful security risk assessment treats risk not as a liability to be feared, but as strategic information to be managed with clarity, ethics, and discipline. It protects your bottom line and your reputation—assets that are incredibly difficult to recover once lost.
A Foundation for Resilience and Trust
Ultimately, this guide reframes the assessment process as the bedrock of your entire security program. By identifying what truly matters—your critical data, key personnel, and essential workflows—you can focus your resources where they’ll have the most impact. It’s about building a culture of security awareness where everyone understands their role in protecting the organization.
When done right, a security risk assessment delivers more than just a report; it provides a clear, actionable roadmap for hardening your defenses. This process empowers you to act fast on early indicators, demonstrate due diligence for compliance, and build an environment of trust with both your employees and your customers.
Defining What You Need to Protect
Before you can even begin a meaningful security risk assessment, you have to answer the most foundational question of all: What are we actually trying to protect? So many organizations fall into the trap of trying to protect everything equally, which just spreads resources thin and leaves the most critical assets vulnerable. The real key is to protect what matters most.
This means you have to get deliberate and collaborative to identify your organization’s “crown jewels.” These aren't just servers or databases; they are the core components that, if compromised, would bring your operations, reputation, or finances to their knees. You have to think beyond just the tangible hardware and software.

A well-defined scope is the absolute bedrock of an effective assessment. It prevents scope creep, focuses your team’s energy, and makes sure your security investments deliver the greatest possible return. Without clear boundaries, an assessment can quickly turn into an endless, resource-draining black hole with no clear endpoint.
Identifying Your Critical Assets
To build a comprehensive inventory, you need to look across four main categories of assets. This process has to involve input from various departments—not just IT—to get a complete picture of what is truly valuable to the business.
Your asset inventory needs to be specific and detailed. For example, instead of just listing "customer data," get granular. Specify the type of data (like PII, payment information, or health records), where it’s stored, and who has access to it.
Data and Information: This is everything from customer personally identifiable information (PII) and financial records to intellectual property like proprietary source code, trade secrets, and strategic business plans.
Technology and Systems: Pinpoint the essential hardware and software that keeps your operations running. This includes critical servers, network infrastructure, cloud services, and any specialized applications vital for day-to-day business.
People and Roles: Don't forget that certain employees and roles are critical assets themselves. Think about key executives, system administrators with privileged access, and specialists whose knowledge is simply irreplaceable for certain business functions.
Processes and Workflows: Map out your essential operational workflows. The process for managing customer payments or the supply chain logistics for delivering your product are critical assets that must be protected from any disruption.
Drawing Clear Boundaries for the Assessment
Once you have a prioritized list of your critical assets, the next step is to draw the boundaries of your security risk assessment. This means specifying exactly which systems, locations, departments, and even third-party vendors will be included. A clear scope statement becomes your charter for the entire project.
A common mistake is treating all vendors the same. A vendor with remote access to your core network presents a far different risk profile than one who supplies office stationery. Your scope must reflect this reality.
To set these boundaries effectively, think about the entire lifecycle and environment of your critical assets. For instance, if your most valuable asset is customer data, your scope has to include every single touchpoint: the web application where it's collected, the cloud database where it’s stored, the internal networks it travels across, and the third-party analytics platforms it might be shared with.
Bringing the Right Stakeholders to the Table
A security risk assessment cannot succeed in a silo. It is fundamentally a cross-functional initiative that needs buy-in and active participation from across the organization. If you fail to involve the right people from the very beginning, you'll end up with critical blind spots and a scope that doesn’t reflect business realities.
Make sure you involve these key departments early in the scoping phase:
Department | Key Contribution to Scoping |
|---|---|
IT and Security | Provides technical details on infrastructure, systems, and existing security controls. |
Human Resources | Offers insights into key personnel, access controls, insider risk concerns, and employee data handling. |
Legal/Compliance | Defines regulatory requirements and data protection obligations that must be met. |
Operations | Identifies critical business processes, workflows, and dependencies that cannot be disrupted. |
By bringing these diverse perspectives together, you ensure the scope of your assessment is not just technically sound but also strategically aligned with the organization's most important operational goals. This collaborative approach turns the assessment from a simple security check into a powerful business enablement tool.
Uncovering Your Real Threats and Vulnerabilities
Once you've mapped out what you need to protect, it's time to figure out what could actually go wrong. This is the discovery phase of your security risk assessment, where you actively hunt for the threats and vulnerabilities that could hit your critical assets. Most teams kick this off with technical scans, which are absolutely essential, but they only tell you part of the story.
Real discovery demands a blended approach. It means looking beyond firewalls and unpatched software to dig into the human element—the procedural gaps and behavioral indicators that automated tools were never designed to catch. This is where a lot of assessments come up short, getting so focused on external attackers that they completely miss the nuanced world of internal risk.

Blending Technical Scans with Human-Centric Analysis
Technical assessments are your first line of defense in spotting weaknesses. These methods systematically poke and prod your digital infrastructure to find known exploits and configuration errors before an attacker does. To get this right, using a complete guide to security audits in network security can give you a solid, structured framework to follow.
The usual suspects in the technical toolkit include:
Vulnerability Scanning: Automated tools that crawl your networks, systems, and apps looking for known security flaws, like outdated software or misconfigured services.
Penetration Testing (Pen Testing): A simulated cyberattack where ethical hackers try to breach your defenses. It’s a real-world stress test of your security posture.
Configuration Reviews: A deep dive into your system settings—from firewalls to cloud services—to make sure they line up with security best practices and your own policies.
But here’s the thing: these tools are fundamentally reactive. They find holes that already exist. They can’t predict what a disgruntled employee might do or spot a conflict of interest that could lead to data theft. That’s why a modern risk assessment has to bring in a human-centric focus.
The Overlooked Factor of Insider Risk
The human element is almost always the most unpredictable—and potent—variable in the security equation. Insider threats, whether they're malicious, accidental, or just negligent, are a leading cause of security incidents. An employee clicking a phishing link out of carelessness or a contractor intentionally walking out with sensitive data are risks a vulnerability scan will never see coming.
This is where a deeper analysis becomes absolutely critical. Instead of just looking at technical logs, you need to examine the procedural and behavioral context around them. You can get a much better handle on this complex area by exploring our detailed guide on the internal threats assessment process.
Your biggest vulnerability isn't always a missing software patch. Sometimes, it's a procedural gap that allows a single person to approve a high-value transaction without oversight or a cultural issue that discourages employees from reporting suspicious activity.
Identifying these human-centric risks requires a different toolkit entirely. It means running workshops with department heads, reviewing internal policies for loopholes, and actually understanding the pressures your employees are under. It's about asking questions like, "Where do our processes rely on a single point of failure?" or "Are there roles with excessive permissions that create an unnecessary risk?"
To paint a clearer picture, let's compare some of the methods used to get a complete view of your threat landscape.
Holistic Threat Identification Methods
Method | Primary Focus | Key Objective | Example Tool/Technique |
|---|---|---|---|
Vulnerability Scanning | Technical Infrastructure | Find and patch known software and configuration flaws. | Nessus, Qualys |
Penetration Testing | System Defenses | Simulate a real-world attack to test security posture. | Metasploit, Burp Suite |
Policy & Procedure Review | Human & Process Gaps | Identify loopholes and single points of failure in controls. | Internal Workshops, Gap Analysis |
Ethical AI Analysis | Behavioral Risk Indicators | Proactively flag patterns that signal potential conflicts or policy bypass. | E-Commander Platform |
As the table shows, a truly comprehensive assessment relies on a mix of tools and techniques. Technical scans provide the foundation, but a deeper understanding of human-driven risk is what gives you a truly resilient security posture.
Identifying Preventive Risk Signals Ethically
Modern platforms give you a way to spot these subtle, human-related risk signals without resorting to invasive surveillance. Ethical, AI-driven systems like E-Commander can analyze structured, work-related data to spot behavioral indicators tied to integrity risks or conflicts of interest. The focus is never on an individual's personal life or intentions but on observable, objective actions that deviate from established policies.
For instance, a system might flag a pattern where an employee consistently bypasses required approval steps for financial transactions. This isn't an accusation of wrongdoing; it's a preventive risk signal. It shines a light on both a procedural vulnerability and a behavioral pattern that warrants a closer, respectful review according to internal governance.
This approach protects employee privacy and dignity while giving the organization a chance to act before an incident happens. It transforms risk management from a reactive, after-the-fact investigation into a proactive, preventive function.
So, you've got a long list of potential threats. That was the easy part.
The real challenge in any security risk assessment isn't finding what could go wrong; it's cutting through the noise to figure out what you need to fix right now. An unprioritized list isn't an action plan. It's just a source of anxiety.
This is where risk analysis saves the day. It’s the structured process that turns a vague sense of dread into a clear, defensible roadmap. Your goal is to focus your team’s finite time, budget, and energy on the handful of issues that actually threaten your organization's survival and success.
Likelihood vs. Impact: The Core of Risk Analysis
At its heart, analyzing risk boils down to two fundamental questions for every single threat you've uncovered:
How likely is this to actually happen?
If it does, how bad will the damage be?
Answering these two questions is what turns a generic threat like "data breach" into a specific, measurable risk scenario. Think about it: a breach caused by a sophisticated nation-state actor is a completely different beast than one caused by an employee accidentally emailing a sensitive file to the wrong person. Each has a different likelihood and a wildly different potential impact on the business.
The threat landscape is always in motion, which constantly changes the likelihood of certain attacks. Even as massive ransomware payouts have recently declined, the overall frequency of cyberattacks has shot up. This shows how criminals are adapting their tactics, moving away from big-game hunting to other advanced attacks. Staying on top of these evolving cyber threat trends in 2025 is critical for accurately gauging likelihood.
Choosing Your Analysis Method: Qualitative vs. Quantitative
There are two main ways to slice this: qualitative and quantitative analysis. Honestly, most organizations start with a qualitative approach. It's faster, more intuitive, and gets the job done for initial prioritization. You can always circle back with a quantitative model for the high-priority risks that need a solid financial justification for new security spending.
A qualitative analysis uses descriptive scales—like low, medium, and high—to score both likelihood and impact. It’s based on expert judgment and collaborative discussion. For instance, your team might agree that the likelihood of a key server failing is "low," but the business impact would be "high."
A quantitative analysis, on the other hand, assigns hard numbers, usually dollar amounts, to risk. This method is far more complex and data-hungry. It involves calculating metrics like Single Loss Expectancy (SLE) and Annualized Rate of Occurrence (ARO) to figure out the Annualized Loss Expectancy (ALE), giving you a concrete financial cost for each risk.
Pro Tip: Don't get stuck in analysis paralysis. Start simple. Use a 3x3 or 5x5 risk matrix with a qualitative approach. This visual tool is perfect for quickly plotting each risk based on its likelihood and impact, making your priorities jump right off the page.
Building a Practical Risk Scoring Framework
A risk matrix is your best friend for turning abstract analysis into a clear priority list. It's a simple, powerful tool that removes guesswork from the equation.
Here’s a straightforward way to build one:
Define Your Scales: First, create clear, objective definitions for your likelihood and impact levels. For example, "High Impact" isn't just a feeling; it could be defined as a financial loss over $1 million, significant reputational damage, and major operational disruption lasting more than 24 hours.
Assign Scores: Next, assign a number to each level (e.g., Low=1, Medium=2, High=3).
Calculate the Risk Score: For each risk you've identified, multiply its likelihood score by its impact score. This gives you a final, comparable number. (Likelihood x Impact = Risk Score)
Establish Risk Tiers: Finally, group the scores into priority tiers. For example, scores of 6-9 might be "Critical," 3-5 "High," and 1-2 "Moderate."
This simple calculation immediately shows you where to focus your attention. A low-likelihood, low-impact risk (1x1=1) naturally falls to the bottom of the list, while a high-likelihood, high-impact risk (3x3=9) shoots straight to the top, demanding an immediate response.
This structured process takes personal bias and gut feelings out of the picture. What you're left with is a defensible, evidence-based roadmap you can confidently present to leadership, showing exactly why certain security investments are non-negotiable.
Developing Your Mitigation and Monitoring Plan
A risk assessment that just ends up as a prioritized list on a spreadsheet is an expensive document, not a defense strategy. The real value comes when you turn those findings into a concrete, living action plan. Once you've identified and ranked your risks, the next move is to build out robust mitigation strategies that align with essential data security best practices to keep your organization safe.
This is where you get down to brass tacks and decide exactly how you'll respond to each high-priority risk. Every threat demands a conscious, documented decision. This ensures your time, budget, and people are focused where they can make the biggest dent in your security posture.
Choosing Your Risk Response Strategy
For every risk you’ve prioritized, your team really only has four fundamental options. Picking the right one is a balancing act, weighing the severity of the risk against the cost of the control and your organization's overall risk tolerance. There's no single "right" answer here; the goal is to make a deliberate, defensible choice for each threat.
These four responses are the core of your action plan:
Avoid: Sometimes, the smartest move is to just get out of the way. This could mean sunsetting a high-risk service, finally decommissioning that ancient, vulnerable server in the closet, or changing a business process to sidestep the threat completely.
Transfer: This is all about shifting the financial impact of a risk to someone else. The classic example here is buying cybersecurity insurance, which helps absorb the massive costs that come with a data breach or another major incident.
Accept: For some risks, the cure is more expensive than the disease. In these cases, you might choose to formally accept the risk, documenting the decision and the logic behind it. This is a perfectly valid strategy for low-impact, low-likelihood risks.
Mitigate: This is where you'll spend most of your time. Mitigation means putting controls in place to reduce the likelihood of a threat happening or to lessen its impact if it does. This is the heart and soul of your active defense system.
Implementing Effective Mitigation Controls
When you decide to mitigate a risk, your next job is to pick the right controls. A strong security program never relies on a single tool. It uses a layered defense—often called "defense in depth"—combining different types of controls to build a resilient barrier against attackers.
These controls typically fall into three buckets:
Technical Controls: This is the hardware and software doing the heavy lifting. We're talking about things like deploying firewalls, rolling out multi-factor authentication (MFA), encrypting data both at rest and in transit, and installing endpoint detection and response (EDR) software.
Administrative Controls: These are the policies, procedures, and training that shape human behavior. This includes having a formal security incident response plan, running regular security awareness training for all employees, and establishing iron-clad access control policies.
Physical Controls: These are the measures that protect your actual, physical stuff. Think security guards, locked server rooms, surveillance cameras, and access badges that keep people out of sensitive areas.
A classic mistake I see all the time is companies over-investing in flashy technical tools while completely neglecting their administrative controls. The most advanced firewall in the world is useless if an employee gets tricked by a sophisticated phishing email. A balanced approach is always the most effective.
Establishing Continuous Monitoring and Review
Security isn't a "set it and forget it" project. It's a continuous process of adapting and improving. The threat landscape changes by the hour, new vulnerabilities are discovered daily, and your own business environment is constantly evolving. Your mitigation plan has to be a living document, not something that gathers dust on a shelf.
You absolutely must establish a rhythm of testing, reviewing, and updating your controls. Not only is this just good practice, but it also creates a clear, auditable trail that proves due diligence and makes compliance with frameworks like ISO 27001 and GDPR much, much simpler.
Your monitoring program should include:
Regular Control Testing: Don't just assume your controls are working. Test them. This means running vulnerability scans, conducting penetration tests, and actually reviewing your access logs on a consistent schedule.
Threat Intelligence Monitoring: You have to stay informed. Keep an eye on new and emerging threats that could target your industry or your specific technology stack.
Annual Review: At a minimum, you need to formally review and update your entire security risk assessment and mitigation plan once a year. You should also do it anytime there's a significant change in your organization, like a merger, a new product launch, or a shift to remote work.
Don't Let Your Assessment Gather Dust—Make It a Living Program
Finishing a security risk assessment isn't the finish line. Far from it. Think of that report as the architectural blueprint for a dynamic, living security program that actually works in the real world. The real win is moving your organization from a reactive, compliance-obsessed mindset to a proactive, strategic one.
This whole process is about building a culture of security awareness and constant improvement. The goal is an environment where early, indicator-based insights protect both your organization and your people from harm. It's time to get away from the annual check-box exercise and into a state of permanent readiness.
Once you've identified and prioritized your risks, you have four primary ways to respond.
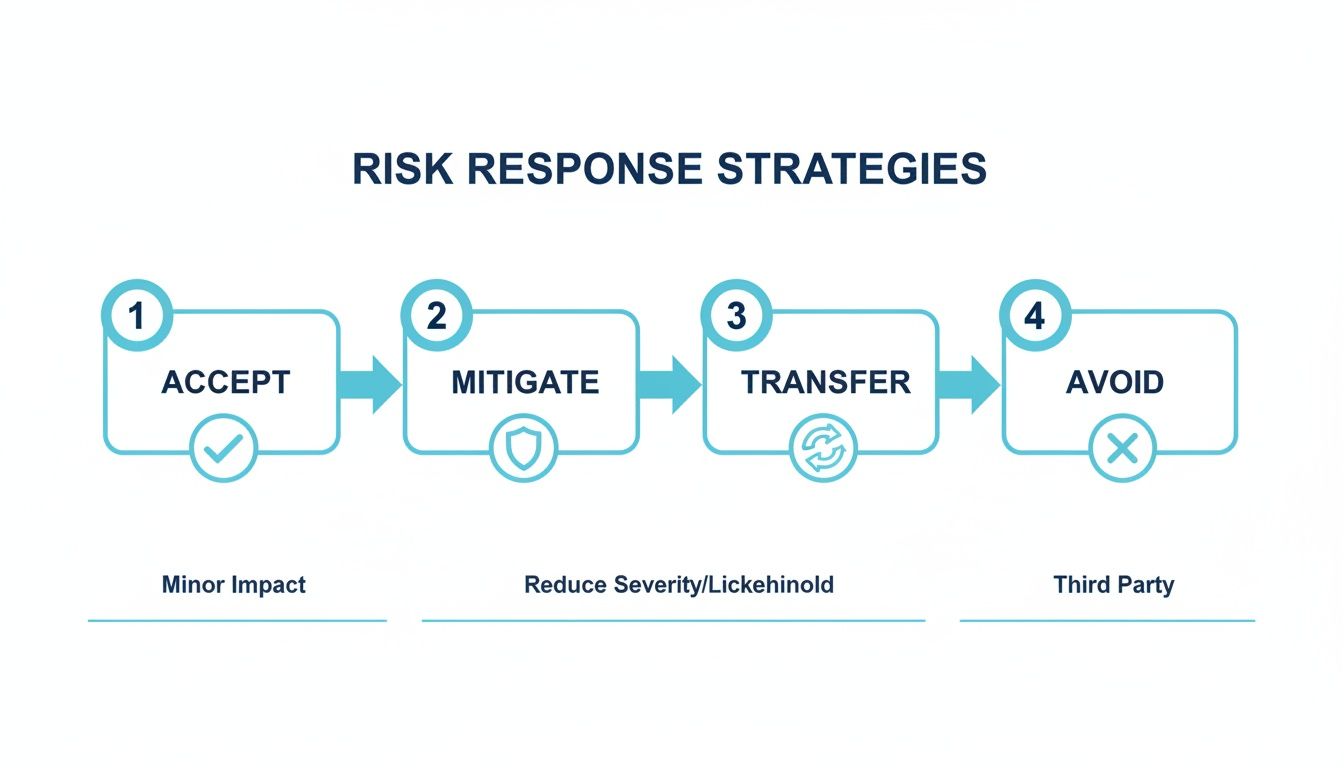
This just goes to show that simply trying to "fix" everything isn't always the right move. Mitigation is just one tool in the toolbox, and every risk deserves a deliberate, strategic decision.
Adopting a Modern, Holistic Approach
A modern security program has to be holistic and humane. It needs to recognize that your greatest risks often bubble up from the complex interactions between people, processes, and technology. This demands a unified view that gets departments like HR, Security, and Compliance out of their silos so they can finally collaborate effectively.
To get there, you need a solid operational risk management framework to provide that essential structure and clarity.
The ultimate goal is to transform risk from a hidden liability into a source of strategic advantage. By knowing first, you can act fast, turning potential crises into opportunities to strengthen organizational resilience and trust.
This proactive stance doesn't mean resorting to invasive surveillance. On the contrary, it relies on ethical tools to identify objective risk signals while preserving employee privacy and dignity. By taking this forward-thinking approach, you create a stronger, more transparent, and more resilient organization that’s ready for whatever comes next.
Got Questions? We’ve Got Answers.
Even with a solid game plan, a few questions always pop up when you're in the thick of a security risk assessment. Let's tackle some of the most common ones we hear from the field.
How Often Should We Run a Security Risk Assessment?
The short answer? A full-blown security risk assessment should be on the calendar at least once a year.
But think of it less like a static annual check-up and more like a living, breathing process. Certain events should automatically trigger a fresh review, no matter when your last one was.
It’s time for another look if you’re:
Bringing on major new technologies or systems.
Going through a big shift in personnel or a company restructure.
Opening new offices or pushing into new markets.
Hearing credible chatter about a new threat targeting your industry.
The best practice is always continuous monitoring. That’s how you stay ahead of the game instead of just reacting to it.
What’s the Difference Between a Vulnerability Assessment and a Risk Assessment?
This is a really important one, and people mix them up all the time. A vulnerability assessment is a deep-dive technical process. It’s all about finding and measuring specific weak spots, like unpatched servers or poorly configured cloud storage. It's a critical piece of the puzzle, for sure.
A security risk assessment, on the other hand, is the whole picture.
A risk assessment takes that vulnerability data, identifies the real-world threats that could exploit those weaknesses, and then analyzes the actual business impact if they succeed. In other words, a vulnerability scan tells you there’s a crack in the wall; a risk assessment tells you what happens if the whole wall comes down.
Is This Really Necessary for a Small Business?
Absolutely. In fact, for a small business, it might be even more important. Attackers love targeting small and mid-sized businesses because they assume security isn't a top priority, making them softer targets.
The scale might be different from a massive enterprise, but the core principles are exactly the same. A formal risk assessment forces an SMB to focus its limited security budget where it matters most, giving you the biggest bang for your buck. Understanding your key assets, the threats you face, and the potential fallout is non-negotiable for the survival of any business, regardless of size.
A modern security risk assessment demands a modern approach. The E-Commander platform from Logical Commander gives you the unified operational backbone to finally shift from reactive checklists to proactive, ethical risk prevention.
%20(2)_edited.png)
