A Clear Insider Threats Definition for Modern Business Risk
- Marketing Team

- Feb 14
- 12 min read
Updated: Feb 16
When business leaders hear "insider threat," they often picture a disgruntled employee stealing company secrets. While that scenario is a real concern, the modern insider threats definition is far broader and more critical for protecting your organization from financial and reputational harm.
An insider threat is not just about malice; it's any human-factor risk originating from an individual with authorized access to your organization's assets. This includes employees, contractors, former staff, or business partners who—intentionally or unintentionally—cause financial, reputational, or operational damage.
A Clear Insider Threats Definition for Modern Business Risk
Viewing insider threats as merely a "cyber" problem is a critical mistake that leaves your organization exposed. This is a fundamental business risk rooted in human behavior, covering everything from deliberate fraud to a simple, costly mistake. The risk starts with people and ends with people.
For leaders in Compliance, Risk, Security, and HR, this perspective is game-changing. It moves the focus away from reactive, invasive surveillance and toward a proactive strategy for managing the entire spectrum of human-factor risk. After all, your biggest vulnerabilities don't always come from external attacks; they are already inside your organization.
Broadening the Scope of Internal Risk
The definition has officially evolved. Authoritative bodies like CISA now clarify that both malicious actors and negligent users are part of the insider threat landscape. This isn't just a change in wording; it reflects the hard data of where the real business damage originates.
In fact, data shows that negligent insiders are behind 55% of all insider incidents, costing companies an average of $8.8 million annually. At the same time, the other 43% of incidents are driven by malicious insiders motivated by revenge, financial gain, or corporate espionage.
This split highlights a massive failure in legacy security approaches.
A security strategy designed to catch a data thief is fundamentally different from one that helps a well-meaning but careless employee avoid mistakes. This nuanced view exposes why a one-size-fits-all surveillance approach fails and underscores the need for intelligent, human-centric prevention.
Ultimately, a complete insider threats definition acknowledges that risk isn't just about intent. A well-meaning employee clicking a phishing link can unleash as much chaos as a malicious one selling intellectual property. This reality demands a new standard of internal risk management—one that's ethical, non-intrusive, and laser-focused on prevention. By understanding the human element at the core of these risks, you can build a more resilient and secure operation. A great starting point is learning how to conduct an effective internal threats assessment.
The Three Faces of Insider Risk
To manage insider risk effectively, you must understand its different forms. A one-size-fits-all security clampdown is doomed to fail because not all insider threats are the same. In fact, most aren't even malicious.
Treating every risk as if it comes from a disgruntled employee leads to invasive, trust-destroying surveillance—a strategy that is often illegal and always counterproductive. True insider risk falls into three distinct categories, and each demands a unique, preventive approach.
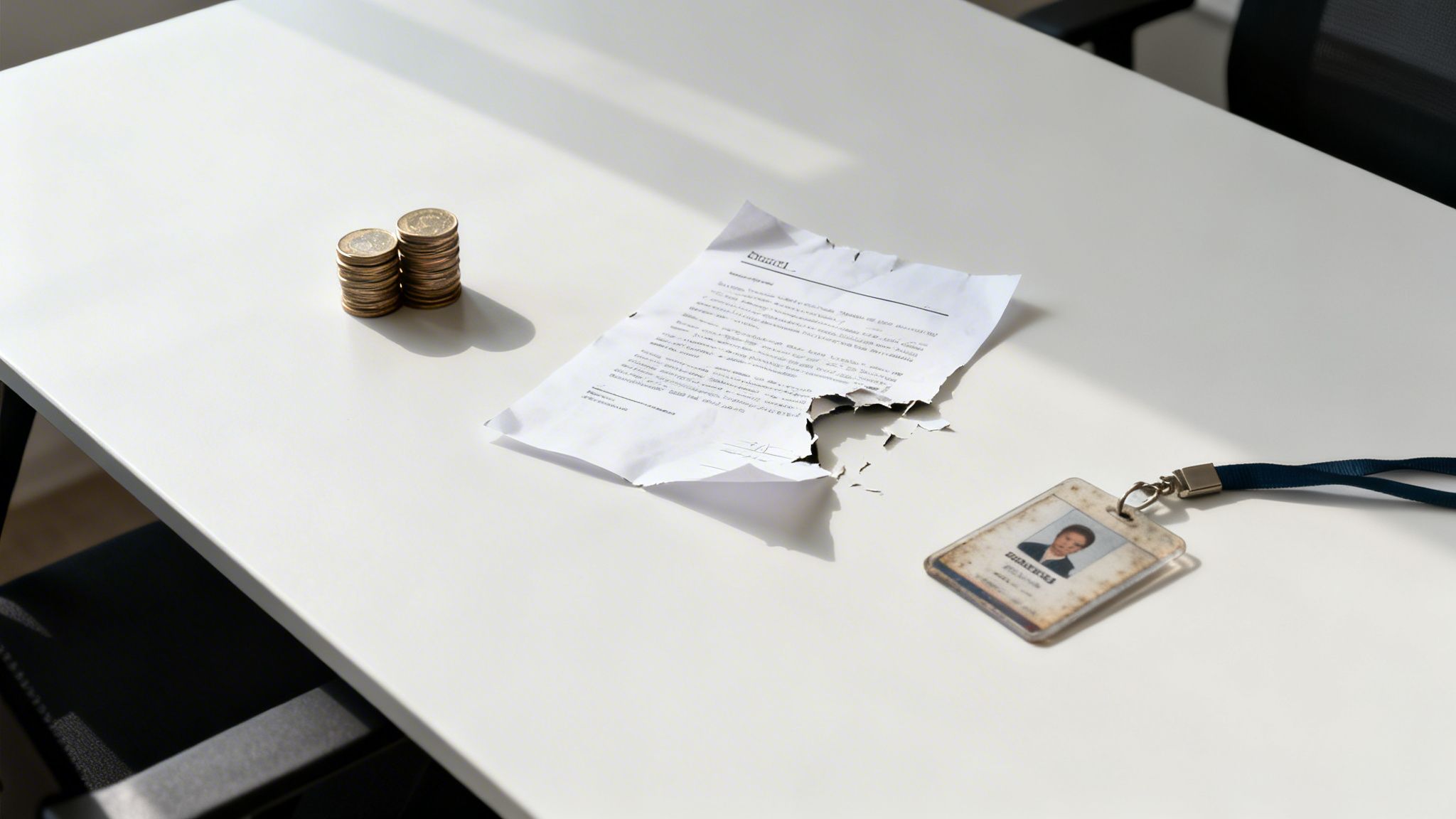
This diagram cuts through the noise, showing how all human-factor risk boils down to two paths: deliberate harm or an unintentional mistake.

This distinction is everything. Recognizing that the root cause is always a human action—whether intentional or not—is the key to building a smarter, more ethical defense.
The Malicious Insider
This is the classic "bad actor" that comes to mind first. It’s the employee, contractor, or partner who knowingly abuses their access to cause damage. Their motivations can range from financial desperation and corporate espionage to revenge after being passed over for a promotion.
A malicious insider is a deliberate threat. They might:
Steal intellectual property to sell to a rival or launch their own competing business.
Sabotage critical systems on their way out the door, fueled by a grudge against management.
Commit fraud by manipulating financial records or customer accounts for personal gain.
These individuals are actively working against your business, making them a serious concern. But they’re only one part of a much larger and more complex risk landscape.
The Negligent Insider
This is the most common—and often most costly—source of insider incidents. The negligent insider is a loyal, well-meaning employee who accidentally puts the company at risk. There’s no malice here, just simple human error, a moment of carelessness, or a lack of security awareness.
These are your trusted team members, which is precisely what makes this threat so dangerous and difficult to manage with old-school tools.
Examples of negligent actions are everywhere:
Falling for a phishing scam and handing over their login credentials to an attacker.
Mishandling sensitive data by accidentally emailing a confidential spreadsheet to the wrong person.
Using weak passwords or leaving a company laptop unsecured in a public place.
A security strategy designed to catch a deliberate data thief is fundamentally different from one that helps a well-meaning employee avoid mistakes. This distinction highlights why invasive surveillance and after-the-fact forensics are inadequate.
The Compromised Insider
The final category is the compromised insider. This is a legitimate employee who becomes an unwilling pawn in someone else's attack. An external hacker has stolen their credentials or gained control of their workstation, often through a phishing attack or malware.
To your security systems, everything looks normal. The attacker uses the employee's account to move through your network, steal data, or deploy ransomware, all while appearing to be a trusted user. The employee may have no idea their identity has been hijacked until it's far too late.
Distinguishing between these three faces of risk is absolutely essential. An approach that only hunts for malicious actors will be completely blind to the far more frequent threats from negligence and compromised accounts. An effective strategy must be smart enough to address the entire spectrum of human risk—and it must do so with an ethical, non-intrusive, and preventive mindset.
The True Cost of Ignoring Human-Factor Risk
When an insider threat materializes, the damage is never just a single data breach or a compliance fine. Ignoring the human-factor risk inside your organization doesn't just leave a door unlocked; it sets the stage for a catastrophic chain reaction that can cripple your finances, reputation, and operations.
The true cost isn't one number—it's a multi-layered crisis that can bring a business to its knees.
The immediate financial hit is staggering. Research from the Ponemon Institute shows that the global average annual cost to clean up after insider incidents has hit $17.4 million per organization.
For companies in North America, the problem is even worse. The cost has nearly doubled in recent years, soaring from $11.1 million to a shocking $22.2 million. The most expensive of these incidents—credential theft—costs nearly $800,000 per event to resolve. You can find more insights on these escalating costs at Proofpoint.com.
Beyond the Balance Sheet
As alarming as those direct costs are, the hidden damages are often far more destructive in the long run. These are the intangible wounds that erode the very foundation of your business and can take years to heal—if they heal at all.
This collateral damage includes:
Reputational Harm: Customer trust is fragile. A public incident involving stolen data or employee misconduct can shatter your brand's credibility, sending clients straight to your competitors.
Loss of Intellectual Property: When trade secrets, product roadmaps, or client lists walk out the door, you lose your competitive edge. This can poison future revenue and knock you out of your market position.
Plummeting Employee Morale: Nothing kills a workplace culture faster than suspicion and lengthy, invasive investigations. Productivity grinds to a halt, and your best employees start looking for the exit.
Operational Disruption: Cleaning up the mess is a massive resource drain. It pulls your key people away from their real jobs, derailing strategic projects and halting innovation for months.
The Failure of Reactive Measures
The message here is crystal clear: reacting after the damage is done is a losing strategy. The costs of forensic investigations, legal battles, and regulatory fines are immense. You can explore a deeper analysis of the true cost of reactive investigations in our related article.
An after-the-fact investigation is an admission of failure. It means the critical systems, processes, and foresight needed to protect the organization were not in place when it mattered most.
This reality reframes proactive prevention not as a cost center, but as a fundamental investment in business resilience and sound governance. Shifting from a reactive posture to a preventive one is the only way to get ahead of human-factor risk and truly protect your organization from the inside out.
Why Old-School Security Tools Fall Short
Many organizations believe their security stack has them covered against insider risks. It's a dangerous—and expensive—assumption. Traditional tools like firewalls, antivirus software, and even Data Loss Prevention (DLP) systems were built with one primary mission: stop external attackers. They are fundamentally blind to the nuances of what authorized users do inside your perimeter.
These systems see the world as "allowed" or "blocked." They'll stop an unauthorized file transfer, but they are useless when a credentialed employee downloads that same file as part of their job. They lack the context to differentiate legitimate work from high-risk behavior, making them unsuited to tackle the human-factor risks at the heart of any true insider threats definition.
The Problem with Surveillance-Based Approaches
In an attempt to close this gap, some companies turn to invasive employee monitoring. This strategy is not just ineffective; it creates a minefield of legal and cultural liabilities. These tools often operate in a legal gray area, pushing against regulations like the Employee Polygraph Protection Act (EPPA) and destroying the foundation of employee trust.
Constant surveillance sends a clear message to your team: "We don't trust you." This crushes morale, kills productivity, and can drive your best people straight to competitors who foster a culture of respect.
Worse yet, these systems unleash a relentless flood of alerts. Security teams wade through thousands of false positives, desperately trying to find a meaningful signal in overwhelming noise. This leads to alert fatigue, where real threats are missed. The problem isn’t a lack of data; it's the absence of actionable, predictive intelligence that can spot risk without violating privacy. You can learn more by exploring different insider threat detection tools and their serious limitations.
Shifting from Reactive to Proactive Prevention
The core failure of old-school security is its reactive nature. These tools are built to catch an incident as it happens or to pick through the digital wreckage after the damage is done. They do nothing to prevent risk from materializing in the first place.
This reactive posture forces organizations into a constant state of defense, always one step behind the next potential incident. To really understand the difference, let’s compare the old, intrusive model with a modern, ethical approach.
Reactive Surveillance vs Proactive Prevention
The table below highlights the stark contrast between traditional, surveillance-based methods and the ethical, proactive model that defines modern risk management. One destroys trust and invites liability; the other builds a culture of integrity.
Attribute | Traditional Surveillance | Ethical Proactive Prevention (Logical Commander) |
|---|---|---|
Focus | After-the-fact detection and forensics. | Identifying behavioral precursors to risk before an incident occurs. |
Method | Invasive monitoring of employee keystrokes, emails, and screens. | Non-intrusive, AI-driven risk assessments based on consent. |
Employee Impact | Destroys trust and creates a hostile, "Big Brother" culture. | Builds a culture of integrity, psychological safety, and accountability. |
Legal Risk | High risk of EPPA, privacy, and labor law violations. | Fully aligned with EPPA, GDPR, and other ethical guidelines. |
Outcome | Massive volume of false positives and crippling alert fatigue. | Actionable, predictive intelligence for targeted, preventive intervention. |
As you can see, the goals are entirely different. One is about catching people; the other is about protecting the organization by getting ahead of problems.
A true solution doesn't require spying on employees. It demands an intelligent, ethical framework that respects privacy while giving leadership the foresight needed to manage human-factor risk proactively.
Adopting the New Standard in Ethical Risk Prevention
Old-school security methods are failing to stop modern insider threats because they were never built to understand the human element. The future of managing this risk isn't about more surveillance. It's about a strategic shift—a move toward ethical, proactive prevention that respects employee dignity and aligns with critical regulations like EPPA.

This new standard leaves the reactive, punitive mindset behind. Instead, it focuses on identifying the behavioral precursors to risk—subtle shifts tied to integrity, ethics, and potential misconduct—long before they snowball into a full-blown crisis. This isn't about policing your staff; it's about protecting the entire organization from the inside out with an EPPA-aligned, non-intrusive alternative.
From Policing to Prevention
Imagine empowering your HR, Compliance, and Risk teams to see potential issues on the horizon without ever reading an employee’s emails or tracking their keystrokes. That's the core of modern AI human risk mitigation. It transforms risk management from a disciplinary function into a strategic pillar for building a stronger, more resilient culture.
The goal is no longer to catch employees making mistakes but to create an environment where those mistakes are far less likely to happen. This requires a solution built on trust, transparency, and a commitment to ethical, non-intrusive methods.
By using an EPPA compliant platform, organizations get actionable intelligence that enables constructive, early intervention. This intelligence isn't based on invasive surveillance. It comes from consented, AI-driven Risk Assessments Software that identifies patterns indicative of elevated risk.
The Power of Proactive Intervention
This forward-looking model lets leadership address potential vulnerabilities constructively. Instead of waiting for a data breach or fraud incident to kick off a costly and disruptive investigation, your teams can take preventive measures, such as:
Targeted Training: Reinforce policies or provide extra security awareness education for specific teams or individuals showing gaps in understanding.
Process Improvement: Pinpoint and strengthen weak internal controls or confusing workflows that might inadvertently create opportunities for error or misconduct.
Supportive Check-ins: Enable managers to engage with team members proactively, offering support and reinforcing expectations before minor issues become major liabilities.
This ethical, prevention-first strategy is the new standard for managing human-factor risk. It not only protects your assets and reputation but also fosters a culture of accountability and psychological safety, turning your workforce into your strongest line of defense.
Take Proactive Control of Your Insider Risk
Knowing the insider threats definition is one thing, but real protection comes from action. Waiting to investigate after something goes wrong is a losing game. Those reactive investigations are too slow and expensive to truly protect your organization.
The only sustainable path forward is a strategic shift to a modern, ethical, and proactive prevention model that addresses the source of the problem: human-factor risk.
By using an AI-driven, EPPA-compliant platform like E-Commander, you can identify the behavioral warning signs of risk without resorting to invasive surveillance. This new standard also includes strong measures for protecting trade secrets to defend your competitive advantage. The entire approach is built on fostering a culture of integrity and accountability, not suspicion.
Don't wait for an incident to expose your vulnerabilities. Adopt the new standard in internal risk management and build a more resilient organization from the inside out.
Instead of just reacting to damage that's already been done, you can take control. This enables constructive interventions that strengthen your defenses for the long run. To see exactly how this works, you might be interested in our deep dive on a complete insider threat framework.
It’s time to move from a defensive posture to a preventive one.
Your Questions About Insider Threats, Answered
When moving from theory to practice, leaders in Compliance, Risk, and HR always have sharp, practical questions. Let's tackle some of the most common ones we hear when building a real-world prevention strategy.
What Is the Difference Between Insider Risk and Insider Threat?
While often used interchangeably, the distinction is critical for your strategy.
Insider risk is the potential for harm from someone with authorized access. It’s a latent vulnerability that exists in every organization by virtue of having a workforce.
An insider threat is what happens when that potential risk becomes a real event. The risk is that an employee could mishandle sensitive data; the threat is when they actually do. A proactive strategy is all about managing the risk to stop the threat before it materializes.
Are All Insider Threats Malicious?
Absolutely not, and this is the most important distinction for decision-makers. The majority of insider incidents are not caused by a "bad actor" trying to sabotage the company.
Recent data shows that 62% of incidents are tied to simple negligence or compromised users. Only 16% come from truly malicious insiders.
This reality is why any strategy focused solely on hunting for bad actors is doomed to fail. The human element is now a primary vulnerability, contributing to roughly 60% of breaches globally. Your prevention plan must address the entire spectrum of human-factor risk, from honest mistakes to deliberate theft. You can see more hard numbers on this by reviewing these comprehensive insider threat statistics.
Can Traditional Security Tools Stop Insider Threats?
For the most part, no. Tools like firewalls and antivirus software were built to stop external attackers from getting in. They are fundamentally blind to the actions of authorized users who are already inside.
Even more specialized tools, like Data Loss Prevention (DLP) or employee surveillance systems, often create more problems than they solve. They’re notorious for generating a storm of false positives, which burns out your security team. Worse, they destroy employee trust and can create massive legal liabilities under regulations like the EPPA. At their core, these tools are reactive—they catch a problem as it’s happening, not before.
What Is an Ethical, EPPA-Compliant Approach?
An ethical, EPPA compliant platform completely changes the game. It shifts the focus away from invasive surveillance and toward proactive, consent-based risk assessment. It steers clear of any methods that resemble lie detection, psychological evaluation, or secret monitoring.
Instead, this modern approach uses AI-driven assessments to identify the behavioral precursors to risk—related to integrity, ethics, and potential misconduct—without ever invading an employee's privacy.
This gives HR, Compliance, and Risk teams the actionable intelligence they need to intervene early and constructively. It's about protecting the organization while respecting its people.
Ready to move beyond reactive investigations and adopt a new standard in ethical risk prevention? Logical Commander offers an AI-driven, EPPA-compliant platform that helps you proactively manage human-factor risk without invasive surveillance.
Discover how our solution provides actionable intelligence to protect your organization from the inside out.
%20(2)_edited.png)
