A Practical Guide to Risk Management in Enterprise
- Marketing Team

- Jan 13
- 15 min read
Updated: Jan 14
Let's be blunt: the old playbook for enterprise risk is failing. A modern approach to risk management in enterprise is no longer a defensive chore siloed in a single department. It's a vital strategic function for building true organizational resilience, protecting stakeholder trust, and driving sustainable growth in a ridiculously complex world.
Why Traditional Risk Management Is No Longer Enough

For decades, risk management operated in neat little boxes. The finance team worried about market volatility, IT focused on cybersecurity, and HR managed personnel issues. Each group had its own language, its own tools, and its own narrow view of the world. This fragmented approach created dangerous blind spots between departments, allowing interconnected threats to slip through the cracks unnoticed—until it was too late.
In today's business environment, that outdated model is completely unsustainable. Companies are now facing a perfect storm of challenges that traditional risk management simply wasn't designed to handle. Rapid digitalization introduces a constant stream of new tech vulnerabilities, while relentless regulatory shifts demand constant vigilance and adaptation.
The Shift from Reaction to Prevention
This new landscape demands a complete strategic overhaul. The goal is to move from reactive firefighting to a unified, proactive strategy that anticipates challenges before they can escalate into full-blown crises. It's about reframing risk management not as a cost center, but as a core driver of operational integrity and a real strategic advantage.
A forward-thinking program does more than just check compliance boxes; it actively strengthens the entire organization from the inside out.
An effective enterprise risk management (ERM) program is built on the understanding that risk is not just something to be avoided, but a critical factor to be managed in the pursuit of strategic objectives. It transforms risk from an unpredictable threat into manageable information.
This proactive stance is more critical than ever. The enterprise risk landscape is experiencing unprecedented complexity, with a staggering 61% of executives reporting that risks are getting more complex. Yet, only 32% rate their own organization's risk oversight as mature or robust. This gap highlights a serious challenge where leaders see the growing danger, but their existing frameworks are struggling to keep pace. You can discover more about these findings on the state of risk oversight.
Core Pillars of a Modern ERM Program
To close this dangerous gap, a modern approach to risk management in enterprise is built on a few key pillars that create a holistic and forward-looking culture:
Unified Governance: Establishing a common language and a single framework for risk that applies to everyone, from the C-suite down to the front lines.
Proactive Identification: Moving beyond the obvious threats to spot the subtle signals of emerging risks, including complex human-capital issues and internal integrity gaps.
Integrated Technology: Using unified platforms to centralize risk intelligence, automate workflows, and provide a single source of truth for all stakeholders.
Shared Responsibility: Creating a culture where every single employee understands their role in identifying and managing risk, turning it into a collaborative, all-hands-on-deck effort.
By building on these principles, organizations can create a resilient foundation capable of navigating uncertainty and seizing opportunities with confidence.
Understanding Modern ERM Frameworks and Concepts
To get a real handle on risk, everyone in the organization has to be reading from the same playbook. This is where Enterprise Risk Management (ERM) frameworks come in. They provide the shared language and structure you need to stop fighting fires in isolated departments and start building a unified, company-wide strategy.
Think of it like building a house. You wouldn’t start without a blueprint, and you definitely wouldn't want the electrician and the plumber working from completely different plans. Frameworks are that master blueprint for your risk management in enterprise program, making sure every team is building toward the same, secure structure.
Defining Your Boundaries: Risk Appetite and Tolerance
Before you can even think about frameworks, you have to get two foundational ideas straight: risk appetite and risk tolerance. They sound similar, but the difference between them is crucial for making clear, consistent decisions.
Risk Appetite is your big-picture, strategic stance. It’s the amount and type of risk your leadership is willing to take on to hit your business goals. For a tech startup chasing rapid innovation, the appetite for risk might be huge. For a buttoned-up financial institution, it will be incredibly small to prioritize stability.
Risk Tolerance is more tactical. It’s the specific, day-to-day wiggle room you’ll accept for a particular risk before you have to act. If your risk appetite is like setting the highway speed limit at 65 mph, your risk tolerance is accepting that your speed might drift between 63 and 67 mph without needing to slam on the brakes.
By clearly defining both appetite and tolerance, leadership provides clear guardrails for the entire organization. This alignment ensures that daily operational decisions consistently support the company's broader strategic goals.
This clarity prevents teams from being either too timid, killing growth, or too reckless, putting the company in harm's way. It's the starting point for any mature conversation about risk.
Choosing Your Blueprint: COSO vs. ISO 31000
With your risk boundaries set, it's time to pick a framework to give your program shape. While plenty of options exist, two giants dominate the field: COSO and ISO 31000. These aren't rigid instruction manuals; think of them as adaptable guides for building a system that actually works for you.
The COSO ERM Framework is a favorite in the U.S., known for its sharp focus on internal controls and tying risk directly to strategy and performance. It’s built around five core components and 20 supporting principles, giving it a very structured feel.
On the other hand, ISO 31000 is a more flexible, principles-based international standard. It’s designed to weave risk management into a company’s existing governance and decision-making fabric, making it incredibly adaptable across different industries and cultures. For more specific guidance within the ISO family, some organizations look into resources like A Practical Guide to Risk Management ISO 27005, which dives deep into information security risks.
The right choice often boils down to your company's culture and specific needs. To help you see how they stack up, here's a quick comparison.
Comparing Leading ERM Frameworks: COSO vs. ISO 31000
Deciding between COSO and ISO 31000 isn't about picking a "winner." It's about finding the best fit for your organization's unique structure, regulatory environment, and culture. The table below breaks down their core differences to make that choice a little clearer.
Aspect | COSO ERM Framework | ISO 31000 Framework |
|---|---|---|
Primary Focus | Internal controls, governance, and linking risk to strategic performance. | Integrating risk management into all organizational activities and decisions. |
Structure | Prescriptive, with 5 components and 20 defined principles. | Principles-based and flexible, providing guidelines rather than rules. |
Ideal For | Organizations needing a structured, audit-friendly approach, especially those with strict regulatory requirements like public companies. | Organizations seeking a highly adaptable framework that can be customized to fit their existing culture and management systems. |
At the end of the day, the best framework is the one your team will actually use. It should create a unified approach that gets different departments working together, not in their own silos.
This idea is the heart of integrated risk management, a concept we explore in our detailed guide: https://www.logicalcommander.com/post/what-is-integrated-risk-management-a-guide-to-proactive-prevention. The real goal is to build a system where everyone shares a common understanding of risk and a collective responsibility for managing it well.
Spotting the Hidden Risks Inside Your Walls
Cyberattacks and market swings get all the headlines, but some of the most devastating threats to your business are already inside. Real risk management in enterprise means turning your attention inward to the complex, often-ignored world of internal threats. This isn't about creating a culture of suspicion. It's about acknowledging a simple truth: human error, negligence, and outright misconduct are risks that can cripple an organization.
These internal blind spots can be far more damaging than any external attack. Why? Because insiders already have the keys to the kingdom—trusted access to your systems, data, and processes. The real challenge is telling the difference between normal day-to-day work and the subtle, early warnings of a problem brewing. Getting ahead of these issues is how you shift from playing defense to building a proactive strategy that protects both your company and your people.
Moving Beyond the Obvious Bad Actor
When most people hear "insider risk," they picture a disgruntled employee sneaking out the door with a hard drive full of secrets. While that certainly happens, the reality of human-element risk is much wider and more nuanced. A truly strong program doesn't rely on invasive surveillance; it looks for structured, objective signals to get ahead of trouble.
This means recognizing the different shades of risk, because each one needs a different solution:
Simple Human Error: Someone accidentally deletes a critical file or gets fooled by a phishing email. These are honest mistakes, but they can still cause massive operational headaches or data breaches.
Negligence: A team member consistently ignores security rules, like sharing passwords or using public Wi-Fi for sensitive work. The vulnerability comes from carelessness, not malice.
Deliberate Misconduct: This is the most sinister category, covering intentional acts like fraud, intellectual property theft, or sabotage for personal gain or revenge.
The infographic below shows how core concepts like risk appetite and tolerance create the guardrails for managing these different threats within a formal ERM program.
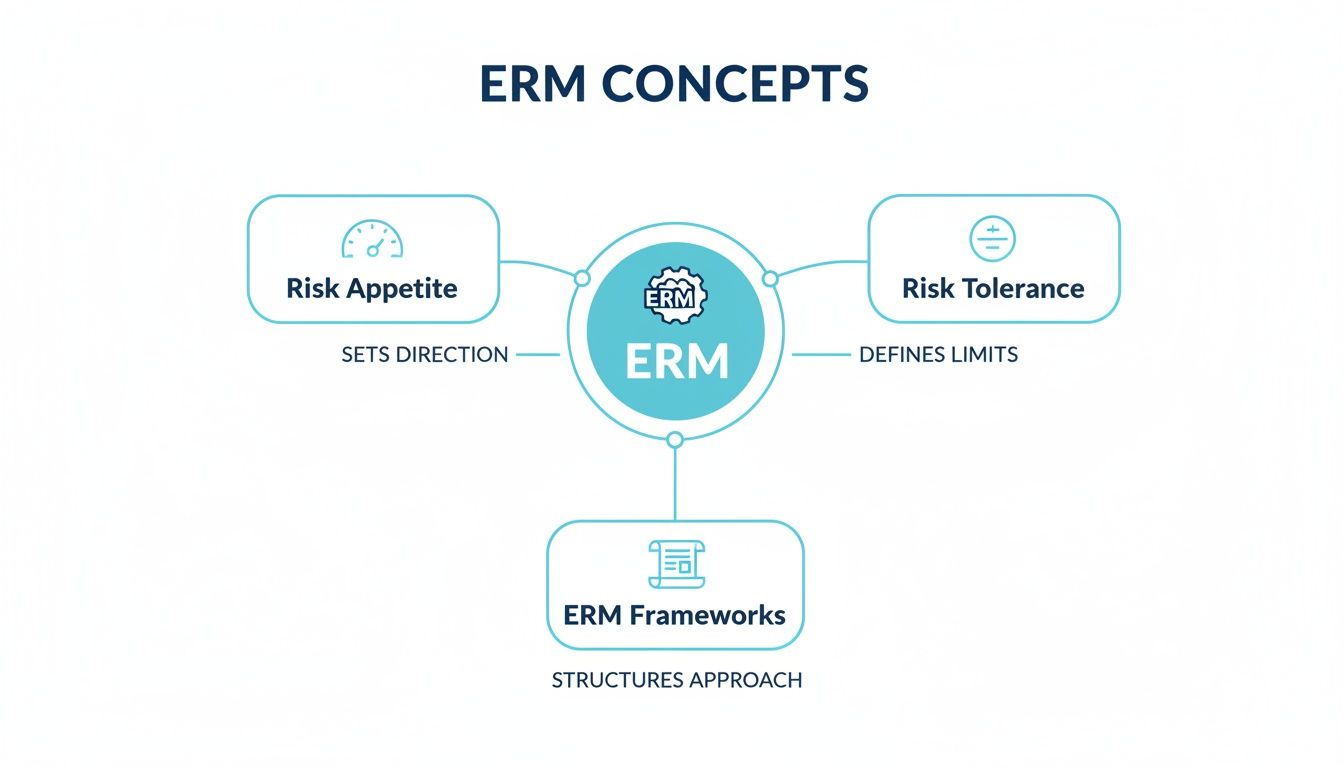
As you can see, you have to set your boundaries (appetite and tolerance) with a clear framework before you can effectively start identifying specific threats.
How to Recognize Early, Objective Signs
The goal of a modern internal risk program isn't to police your employees. It's to identify objective risk indicators that point to a potential problem, protecting employee privacy while strengthening the organization. It’s about spotting patterns, not judging people. For instance, to counter potential operational failures, smart businesses implement robust strategies for multi-provider failover reliability to keep things running smoothly.
Effective insider risk programs are built on trust and transparency. The goal is to find systemic weak points and organizational pressures before they lead to misconduct, creating a safer environment for everyone.
This proactive stance is becoming non-negotiable. Insider and third-party threats are now gaping holes in corporate defenses. In fact, 46% of organizations are planning to increase their investment in insider risk programs. Yet, a shocking 48% of companies are still tracking third-party risk on outdated spreadsheets, and 41% have already been hit by a major third-party breach. This reliance on disconnected, manual processes is just asking for trouble.
Key Areas for Proactive Identification
To build a truly preventative strategy, you need to focus on structured signals in a few key areas. These indicators are objective and can be flagged through controlled, ethical processes—no invasive monitoring needed.
Conflicts of Interest: Systematically cross-referencing your vendor lists against employee databases. This can flag undisclosed financial ties that could compromise the integrity of your procurement process.
Unusual Pressure: Identifying employees in high-stakes roles who might be under extreme financial or personal stress, as this can be a powerful motivator for misconduct. This is done through structured, policy-driven reviews, not by snooping into personal lives.
Ethical Drift: Noticing gradual slips from company policy or ethical codes. Think bypassing required approvals or mishandling sensitive data. These small deviations can signal a bigger decline in integrity.
By focusing on these objective signals, you can step in early with support, extra training, or simple process fixes. This transforms risk identification from a punitive hunt into a supportive function that reinforces a culture of integrity and protects the entire business from preventable harm.
Using Technology to Unify Your Risk Strategy

Let's be blunt: you can't run a modern enterprise risk strategy with last-generation tools. If your team is still juggling disconnected spreadsheets, siloed software, and manual reporting, you’re creating dangerous blind spots. Critical insights get buried, and by the time you spot a problem, it’s already too late.
To move from theory to effective execution, you need technology that rebuilds your risk management capability from the ground up.
This is where a unified operational platform becomes your central nervous system for risk. Forget fragmented data; this approach creates a "single source of truth" that brings all your risk intelligence into one place. Suddenly, HR, Compliance, and Security aren't operating in isolation. They're collaborating in one environment, sharing data and insights in real time.
This centralized model demolishes the departmental walls that have historically crippled risk management in enterprise. The result is a complete, holistic view of organizational threats, empowering faster and far more informed decision-making.
The Power of a Unified Platform
A unified platform is more than a digital filing cabinet. It operationalizes your entire risk strategy, connecting every piece of the puzzle to ensure your frameworks are applied consistently across the entire business. The benefits are immediate and substantial.
Here’s what it brings to the table:
Centralized Risk Intelligence: All risk data—from incident reports to audit findings—is consolidated in one secure hub. This kills off conflicting information and gets everyone working from the same playbook.
Automated Workflows: Routine tasks like notifications, escalations, and evidence collection can be automated. This frees up your teams to stop chasing paperwork and start focusing on high-value strategic analysis.
Streamlined Reporting: With all your data in one place, generating custom reports and dashboards for stakeholders—from front-line managers all the way to the board—becomes a simple, efficient process.
This kind of real-time visibility is what proactive risk management is all about. It lets leaders spot trends and stamp out issues before they can escalate into a full-blown crisis. You can explore a variety of modern enterprise risk management tools that offer these integrated capabilities.
Using AI Ethically and Effectively
Any conversation about technology in risk management quickly turns to Artificial Intelligence. AI holds immense potential, but its use demands strict ethical discipline. The goal isn't to replace human oversight; it's to augment it.
An ethical AI system in risk management is designed to spot objective, structured risk indicators—it does not make judgments, profile individuals, or analyze behavior. For example, it might flag a potential conflict of interest by cross-referencing vendor and employee databases based on predefined rules. It would never monitor private communications or try to predict someone's intent.
The right technology is a decision-support tool, not a decision-maker. It surfaces objective signals for human review, ensuring that due process, privacy, and dignity are always preserved under established governance policies.
This approach is grounded in "privacy-by-design" principles aligned with regulations like GDPR. The growth in this space is massive; the broader governance, risk, and compliance (GRC) software market hit $38 billion in 2024 and is projected to skyrocket to $138 billion by 2030.
Yet, despite this momentum, only a startling 6% of organizations currently use AI to help identify risks, revealing a major capability gap that leaves them exposed.
By adopting technology built on these ethical foundations, you can turn it into a powerful ally for effective and responsible risk prevention. It finally transforms risk management from a reactive, manual chore into a proactive, data-driven strategic function.
Building a Culture of Shared Risk Responsibility
Frameworks and technology give you the skeleton for a strong risk program, but they’re just tools. Real organizational resilience comes from a culture where every single employee feels a sense of ownership over risk.
When that happens, risk management in enterprise stops being a top-down mandate and becomes a living, breathing part of the company's DNA.
Building this kind of culture isn’t about spreading fear or suspicion. It’s about creating an environment of psychological safety where people are not only empowered but actively encouraged to flag potential issues, ask tough questions, and voice concerns without fearing blame. This is when risk management truly becomes everyone’s job.
Secure Clear Leadership Buy-In
A culture of shared risk responsibility lives and dies with leadership. If the C-suite isn't bought in—visibly and consistently—any effort to decentralize risk ownership is doomed to fail. Leaders have to do more than just sign off on a policy; they have to champion it.
This means they need to talk about the strategic importance of risk management all the time—in town halls, team meetings, and company-wide emails. Their actions must shout the message that managing risk is a core business function, not just a box-ticking exercise for the compliance department. Our article on the "tone from the top" digs into how leadership behavior shapes culture, and you can learn more about its impact on risk management here.
A risk-aware culture only thrives when leaders model the right behaviors. When an executive openly discusses risks and owns up to mistakes, they send a powerful signal that transparency and accountability matter more than anything else.
That visible commitment from the top is the foundation for everything else. It’s the essential first step to weaving risk awareness into the fabric of your organization.
Define Roles with the Three Lines of Defense
Once leadership sets the tone, the next step is to give that cultural vision a clear, operational structure. One of the most effective models for this is the "Three Lines of Defense." It’s a simple but powerful framework that clarifies who is responsible for what, preventing confusion and making sure there are no gaps in your risk oversight.
First Line of Defense: These are your front-line people—the managers and employees who own and manage risk as part of their everyday jobs. They’re responsible for spotting risks and putting controls in place. For example, a sales manager owns the risks tied to customer contracts and data handling.
Second Line of Defense: This group provides expert oversight. Functions like Compliance, Security, and the central Risk Management team set policies, provide tools, and check on how well the first line's controls are working. They help the first line manage risk effectively without taking ownership away from them.
Third Line of Defense: This is Internal Audit. Operating independently, this line gives objective assurance to senior management and the board that the first two lines are actually working as they should. They’re the ultimate check and balance in the system.
This model transforms risk management in enterprise from a vague concept into a clearly defined, shared responsibility.
Deliver Training That Actually Sticks
Finally, a strong culture depends on effective, continuous training. Let's be honest: generic, check-the-box annual training is a waste of time. To make an impact, training has to be tailored, practical, and directly relevant to an employee's specific role.
Ditch the dry policy readings and use real-world scenarios and interactive workshops instead. A finance team member needs completely different risk training than a software developer.
When you make the training specific and actionable, you empower your employees to become your best risk sensors. Their daily awareness becomes a powerful protective shield for the entire organization.
How to Measure and Report on ERM Success
So, how do you actually prove your enterprise risk management program is working? Success isn't just about the disasters you manage to sidestep; it's about the quality of your decisions and the resilience you build into the very fabric of the organization. To show real value, you have to move beyond a simple "pass/fail" compliance mindset.
This means you need to stop focusing only on defensive metrics. The real goal is to connect the dots and show how risk management in enterprise is actively helping hit strategic goals. You want to turn risk data from a static, backward-looking document into the kind of intelligence that drives smart, forward-looking conversations about where the business is headed.
Defining Your Key Indicators
To get a clear picture of success, you need to track two different but deeply connected types of metrics: Key Performance Indicators (KPIs) and Key Risk Indicators (KRIs). They sound similar, but they tell different parts of the ERM story.
Key Performance Indicators (KPIs) are all about the health of your risk management processes. They tell you how well your program is actually running.
Key Risk Indicators (KRIs) are your early-warning system. These are predictive metrics that signal a rising risk exposure that could throw you off course if you don't act.
Here’s a simple way to think about it: A KPI is like checking the oil level in your car—it’s a measure of how well you're keeping up with maintenance. A KRI is the oil pressure warning light flashing on your dashboard, telling you a problem is developing right now.
By tracking both KPIs and KRIs, you get the full story. You can see how well your program is running today (KPIs) while keeping your eyes on the road ahead for any trouble spots (KRIs).
Crafting Reports for Different Audiences
A generic, one-size-fits-all risk report is almost always a waste of time. The information a front-line manager needs is worlds away from what the board of directors cares about. Tailoring your reports and dashboards is the only way to make the data hit home for each group.
Here’s a practical way to break it down:
For the Board of Directors: Keep it high-level and strategic. They need the big picture: the organization's overall risk profile, how it lines up with the agreed-upon risk appetite, and the top emerging threats that could derail long-term plans. Visual dashboards that show trends over time are your best friend here.
For Senior Leadership: Give them executive summaries that tie risk data directly to business performance. They need to see key risk trends, the status of your big mitigation projects, and the real financial impact of risk events. This group needs to understand how risk management makes their strategic decisions better and safer.
For Front-Line Managers: Get granular and operational. These reports should focus on the specific risks humming away in their department, how effective their controls are, and any action items that are still open. The goal is to give them the tactical intel they need to manage risk in the trenches, day in and day out.
Got Questions About ERM? We've Got Answers.
When you're building out an enterprise risk management framework, you’re bound to run into some practical questions. Let's dig into a few of the most common ones we hear from leaders who are trying to get it right.
Where Do We Even Start with Implementing ERM?
The absolute first step? Get your executive team on board. Without genuine sponsorship from the top, any ERM program is dead in the water—it'll lack the authority and the resources to make a real impact.
Once you have that commitment, your next move is to pull together a cross-functional team. You need people in the room from HR, Legal, IT, and Operations. This isn't just a finance or compliance issue; it’s an everyone issue. Their first job is to map out your organization's unique threat landscape. This foundational work lets you build a strategy and risk appetite statement that actually fits your business, instead of just copying some generic template.
How Can We Use AI Ethically Without Being Creepy?
This is a huge one, and it's where a lot of companies go wrong. Ethical AI in risk management in enterprise is about analyzing objective, structured data to flag predefined risk indicators. It is not about surveillance or behavioral profiling.
Think of it this way: an ethical AI system might flag a potential conflict of interest by cross-referencing a vendor database with an employee list. It would never monitor private chats or make moral judgments about an individual.
The key is using AI as a tool to support human judgment. It surfaces potential issues for review, all under the umbrella of strict privacy policies like GDPR. Technology should sharpen your governance, not replace it.
How Do We Get Our Siloed Departments to Work Together on Risk?
Breaking down silos takes a mix of the right process and the right technology. From a tech standpoint, implementing a unified operational platform is a game-changer. It creates a "single source of truth" where all risk-related data, workflows, and reporting live. This is how you get HR, Security, and Compliance working seamlessly in one system instead of three.
But the tech is only half the battle. You have to back it up with a solid governance structure that creates a common risk language for the whole organization. This structure needs to define clear roles and make sure everyone is pulling in the same direction, turning a bunch of isolated efforts into a coordinated, resilient defense.
At Logical Commander Software Ltd., we provide a unified operational platform designed to help you proactively manage internal risks ethically and effectively. Our AI-driven system identifies objective indicators without surveillance, allowing you to build a resilient organization while upholding employee dignity and privacy. Discover how to strengthen your enterprise risk management strategy.
%20(2)_edited.png)
