A Clear Definition of Insider Threats for Business Leaders
- Marketing Team

- Feb 15
- 16 min read
Updated: Feb 16
An insider threat is far more than just another cybersecurity buzzword. It's a critical human-factor risk, and it originates from the very people you trust with authorized access to your organization's most sensitive data and systems.
This includes current and former employees, contractors, and even business partners. Whether their actions are intentional or completely accidental, the result can be the same: significant financial, operational, and reputational damage. This is a human problem, not a cyber problem, and it requires a new standard of proactive, ethical prevention.
Defining Insider Threats Beyond the Textbook Answer
When Compliance, Risk, and Security leaders sit down to talk about the real-world definition of insider threats, the conversation has to move past simple IT explanations. An insider threat isn't just about stolen data; it's a fundamental business risk that directly impacts liability, governance, and shareholder value.
At its core, it’s a security event that starts from inside the organization, specifically from an authorized user who has legitimate access. It is a human-factor risk that traditional security tools, which focus on external attackers, are blind to.
These threats aren't monolithic. They break down into two main categories: malicious insiders, who deliberately misuse their access for personal gain or disruption, and negligent insiders, who expose data through simple carelessness or a lack of security awareness. You can explore these categories further in research from UNC Charlotte. This distinction is crucial because it proves the risk isn't limited to a few "bad apples"—it’s a vulnerability that exists across the entire workforce and demands a proactive, not reactive, strategy.
The Three Faces of Insider Threats
To get a real handle on this human-factor risk, you have to understand the three distinct types of insiders. Each one presents a unique challenge that demands a different strategy—one that older, reactive security tools are completely unprepared to handle. A truly proactive, EPPA-aligned approach has to account for the full spectrum of human behavior without resorting to invasive surveillance.
To make this crystal clear, here’s a quick breakdown of the three primary insider threat profiles.
Threat Type | Motivation or Cause | Common Example |
|---|---|---|
The Malicious Insider | Intentional harm, often driven by revenge, financial gain, or competitive advantage. | A disgruntled engineer sabotages a critical system on their way out the door. |
The Negligent Insider | Unintentional carelessness, lack of training, or simple human error. | A well-meaning employee falls for a sophisticated phishing email and exposes company credentials. |
The Compromised Insider | An external attacker steals and uses the credentials of a legitimate, unsuspecting employee. | A cybercriminal uses a stolen password to log in and move undetected through the network. |
Understanding these different faces is the first step. The real challenge is preventing the damage before it occurs.
The core problem is that all three types of insiders operate with legitimate credentials, making them nearly invisible to traditional security tools. Legacy solutions that rely on surveillance or after-the-fact investigations are not only invasive but also fail to prevent the incident. This is why a new standard of ethical, AI-driven prevention is necessary to identify pre-incident indicators before damage occurs.
Ultimately, a modern definition of insider threats must frame the problem in terms of preventable business impact. It shifts the entire focus from costly, after-the-fact investigations to proactive, EPPA-aligned prevention that protects the organization while respecting its employees.
Understanding the Real Business Impact of Internal Risks
Insider threats need to be more than a line item on a security checklist; this has to be a boardroom-level conversation. Why? Because these risks aren't theoretical. They translate directly into tangible financial and operational consequences that can paralyze a business. An unmanaged internal risk program isn't just a compliance gap—it's a massive liability that eats into profitability, shareholder value, and your brand's integrity.
For leaders in Compliance, Risk, and Legal, the connection is painfully clear. Unaddressed human-factor risks are a direct pipeline to steep financial losses, regulatory penalties, and reputational damage. The cost isn't hypothetical; it's a quantifiable drain on resources that far exceeds the investment needed for proactive prevention.
The Staggering Financial Drain of Insider Incidents
The financial damage from insider-led incidents has climbed to record highs, making it an undeniable priority for any enterprise. Recent data shows that insider threats now cost organizations an average of $17.4 million a year, up from $16.2 million the previous year. This isn't a fluke; it's a clear upward trend showing that reactive measures are failing and these events are hitting harder.
This financial burden is directly tied to how long it takes to contain them. On average, it takes a staggering 86 days to identify and contain an insider threat. For incidents that fly under the radar for over 90 days, the average annual cost skyrockets to $18.33 million. Every single day of delay dramatically inflates the damage.
The infographic below breaks down where these incidents come from.
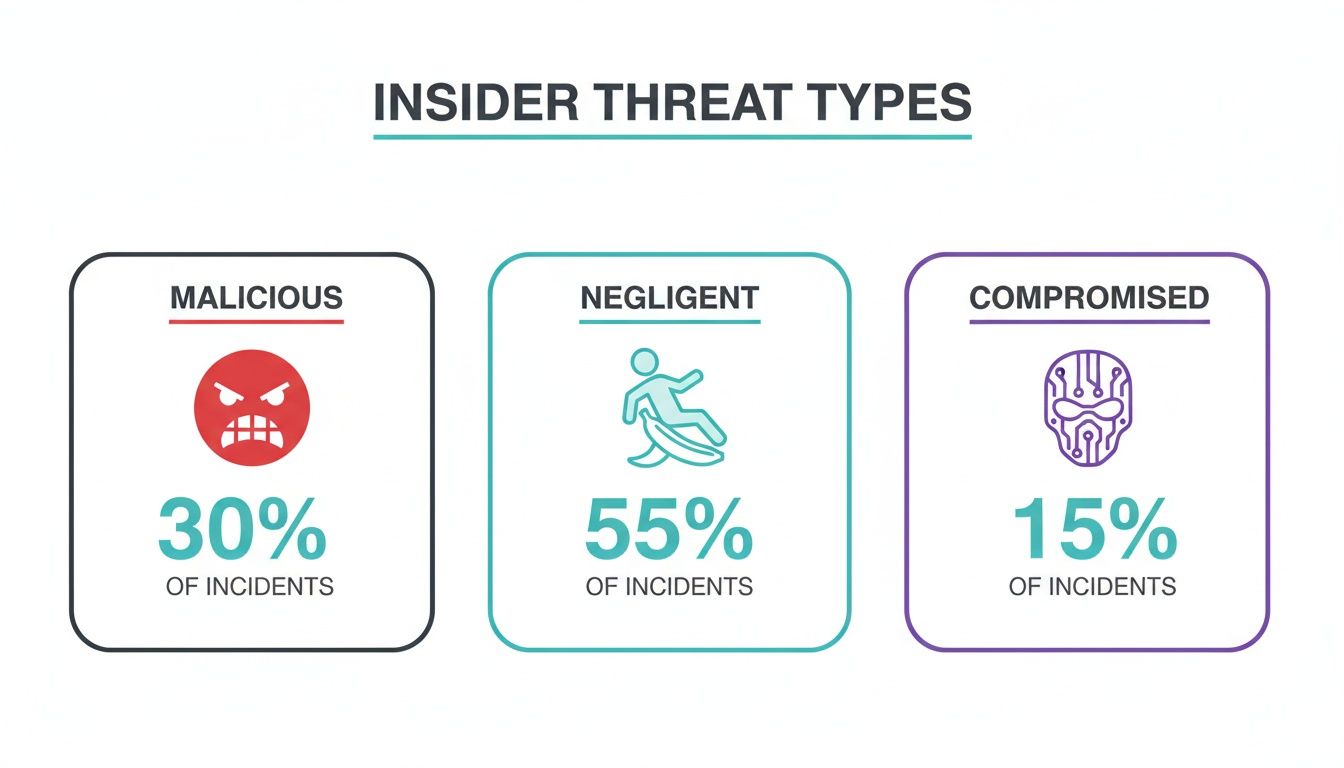
This data highlights a critical insight: simple negligence is the most frequent source of insider incidents, making it the primary driver behind these multi-million dollar costs. This proves that a strategy focused only on malicious actors is destined to fail.
Beyond the Balance Sheet: Operational and Reputational Costs
The damage from an insider threat goes way beyond the direct financial hit. The operational fallout can be just as devastating, disrupting core business functions and pulling critical resources away from growth. When an incident happens, the entire company's focus shifts to costly, time-consuming reactive investigations.
These investigations create a ripple effect of disruption across multiple departments:
Legal and Compliance Teams get pulled into complex internal reviews and potential litigation.
HR Departments are forced to manage difficult employee situations and address a collapse in morale.
Security and IT Staff are diverted to forensic analysis and system remediation instead of strategic projects.
This internal paralysis is a huge hidden cost. Worse, every incident chips away at an organization's most valuable asset: its reputation. A public breach erodes trust with customers, partners, and investors, leading to long-term brand damage that can take years, if ever, to fully repair.
The true cost of an insider threat is never just the dollar amount of the initial incident. It is the sum of financial loss, operational disruption, regulatory fines, and the slow erosion of stakeholder trust. This is why a proactive, preventive framework is not just a best practice—it's a financial and strategic necessity.
These mounting costs underscore an urgent need for a new approach. Waiting for an incident to happen before taking action is no longer a viable strategy. You can learn more about why post-incident reviews are failing modern businesses by exploring the true cost of reactive investigations. Adopting a proactive, ethical risk management program is the only way to mitigate these enormous costs and protect your organization's future.
Why Traditional Detection Methods Are Failing Businesses
For years, companies have relied on a standard playbook for internal risks, one built on the idea of catching bad actors after the fact. This model leans heavily on digital forensics and post-incident investigations, but it’s fundamentally broken. Its biggest flaw? It’s completely reactive—it only kicks into gear after the damage is done, leaving Compliance, Risk, and Security teams to clean up a mess that could have been prevented.
These old-school strategies aren't just slow; they were never designed for the modern definition of insider threats. They were built to find external hackers, not to understand the nuanced behaviors of trusted people. This mismatch creates a costly and ineffective cycle that never gets to the root cause of the risk—the human factor.
The High Cost and Low Return of Reactive Forensics
When an incident hits, the typical response is to launch a forensic investigation. This process is a massive drain on resources, often requiring specialized tools and expensive consultants that make costs spiral out of control. These investigations can drag on for months, pulling key people away from their jobs and causing huge operational disruptions. According to IBM, it takes an average of 86 days just to contain an insider-led incident—a delay that directly inflates the final bill.
Worse, these methods often put companies in a legally dangerous position. Many older security tools rely on invasive surveillance and employee monitoring that can easily violate privacy and run afoul of regulations like the Employee Polygraph Protection Act (EPPA).
Relying on post-incident forensics is like installing a smoke detector that only goes off after the building has already burned down. It confirms a disaster happened but does nothing to prevent it, leaving the organization to bear the full financial and reputational cost of the damage.
This reactive posture creates a culture of distrust and fails to distinguish between malicious intent and simple human error, treating every incident like a crime scene.
A New Standard: Proactive Prevention
The glaring flaws in these outdated methods show why we urgently need a new standard. Modern internal risk management demands a proactive and preventive strategy—one that is ethical, non-intrusive, and focused on spotting risk indicators before they escalate into costly events. Instead of waiting for a policy to be broken, a forward-thinking program identifies the precursors to risk.
This shift from reaction to prevention is a massive strategic upgrade. The table below highlights the critical differences between the old, broken model and the new standard of proactive, ethical risk management.
Reactive Forensics vs Proactive Prevention
Attribute | Traditional Reactive Methods | Modern Proactive Methods |
|---|---|---|
Timing | Post-incident; after damage occurs. | Pre-incident; before damage occurs. |
Focus | Forensic investigation and remediation. | Risk identification and prevention. |
Employee Impact | Creates a culture of suspicion and distrust. | Fosters a culture of integrity and support. |
Legal Risk | High; often involves invasive surveillance. | Low; EPPA-aligned and non-intrusive. |
Cost | Extremely high investigation and recovery costs. | Low, predictable investment in prevention. |
Moving from reaction to prevention isn't just an improvement; it's a necessary evolution for survival. As you assess your own program, think about how modernizing your approach can better protect your organization. Our guide on advanced insider threat detection tools offers deeper insights into making this critical transition.
Ultimately, a proactive framework built on AI-driven, ethical human risk management protects the organization without compromising employee dignity, setting a new and much-needed standard for corporate governance.
Breaking Down the Three Types of Insider Threats
To get beyond a generic definition of insider threats, you have to understand the human scenarios behind them. An insider threat isn't one type of person or event; it's a spectrum of human-factor risks, and they show up in very different ways. For leaders in Compliance, HR, and Security, seeing these distinctions is the key to building a prevention strategy that’s both effective and ethical.
These threats generally fall into three buckets: the malicious insider, the negligent insider, and the compromised insider. While their motivations are worlds apart, they all share one dangerous trait—they operate with legitimate, authorized access. This makes them incredibly hard to spot with traditional security tools designed to keep attackers on the outside.

Let's unpack the real-world business examples behind each label to make these abstract ideas tangible.
The Malicious Insider: The Deliberate Saboteur
The malicious insider is the classic villain of the story. This is someone who intentionally uses their authorized access to harm the organization. They’re often driven by revenge, financial desperation, or a plan to gain a competitive edge. Their actions are premeditated and designed to cause maximum damage.
Think about these all-too-common scenarios:
Data Theft for a New Job: A top salesperson accepts an offer from a direct competitor. Before they turn in their notice, they download the entire client database, contact lists, and proprietary sales playbooks to a personal device. They plan to walk into their new role with a massive, unfair advantage.
Sabotage by a Disgruntled Employee: An engineer who was just passed over for a promotion or put on a performance improvement plan decides to get even. They use their system credentials to quietly introduce bugs into a critical software update or delete key project files, sparking operational chaos and costing the company a fortune.
These actions are born from clear intent. But a strategy that just waits for the damage to happen before punishing someone has already failed. A proactive program has to identify the pre-incident indicators of high-risk behavior before these plans are ever set in motion.
The Negligent Insider: The Unintentional Risk
Far more common—and often more costly—is the negligent insider. This person has zero malicious intent. They inadvertently create a security hole through simple carelessness, a lack of awareness, or by sidestepping policy for the sake of convenience. Their actions aren't meant to cause harm, but the consequences can be just as devastating as a deliberate attack.
This distinction is critical for risk management. While malicious insiders grab headlines, it's the negligent ones who are behind the majority of all incidents. This tells us that most insider risk comes from unintentional mistakes, not deliberate sabotage. This statistical reality is why organizations are finally starting to invest heavily in modern insider risk management. You can learn more about these insider threat statistics and their impact.
Here’s what negligence looks like in practice:
Falling for a Phishing Scam: A finance employee gets a convincing but fake email that looks like it's from a trusted vendor. They click a malicious link, unknowingly handing an external attacker the keys to their login credentials and the company's financial systems.
Mishandling Sensitive Data: An HR manager, working from a coffee shop, emails a spreadsheet full of employee salaries and personal information to their personal email account to finish up some work. This simple act violates data handling policies and puts highly sensitive PII at serious risk.
The challenge with negligent insiders is that punitive measures don't work and only destroy morale. The solution is a non-intrusive, supportive approach that finds procedural gaps and offers corrective guidance before a simple mistake becomes a multi-million-dollar breach.
The Compromised Insider: The Unsuspecting Pawn
Finally, we have the compromised insider. This is a legitimate employee whose credentials have been stolen by an external attacker. This person is an unwitting victim, but their account becomes a powerful weapon for cybercriminals. Once inside, the attacker can move through the network disguised as a trusted team member, accessing data and systems without tripping the alarms of traditional perimeter defenses.
This scenario usually plays out in a couple of key ways:
Credential Stuffing: An attacker gets their hands on a list of usernames and passwords from a data breach at another company. They then try those same credentials on your corporate network. If an employee reused their password, the attacker gets instant access.
Malware Infection: An employee connects their work laptop to an unsecured public Wi-Fi network, and it gets infected with keylogging malware. The malware quietly captures their login credentials and sends them straight to the attacker.
In these cases, the employee isn't at fault, but their compromised identity becomes the gateway for a major security incident. This highlights the absolute need for a system that can spot anomalous account behavior, even when the credentials being used are technically valid. An ethical, AI-driven platform provides this crucial layer of defense without resorting to invasive surveillance of your team.
Adopting a New Standard for Ethical Risk Prevention
The traditional ways of managing internal risk are fundamentally broken. They’re built on a reactive foundation of invasive surveillance and costly forensics—methods that only kick in after the damage is done. This outdated model is completely out of step with the modern definition of insider threats, which encompasses a whole spectrum of human-factor risks, from deliberate malice to simple, honest mistakes.
We urgently need a new standard. One that's built for prevention, not just punishment, and is ethical by design.
This new approach throws out the legally toxic practice of employee surveillance. Instead, it focuses on identifying the behavioral warning signs of risk in a way that is non-intrusive and respectful. It’s about protecting the organization and its people, creating a culture of integrity instead of one of suspicion.

Prioritizing Ethics and EPPA Alignment
The cornerstone of this modern approach is an unshakeable commitment to ethical principles and regulatory compliance, especially with the Employee Polygraph Protection Act (EPPA). Many so-called "insider threat" tools operate in a dangerous legal gray area, using methods like secret monitoring, keystroke logging, or other forms of employee surveillance. These invasive techniques expose organizations to massive liability and create a toxic work environment.
The new standard rejects this model entirely. An EPPA-aligned platform like Logical Commander operates without ever crossing these critical legal and ethical lines.
No Surveillance or Secret Monitoring: The system doesn't spy on employee emails, track keystrokes, or watch daily activities. It respects privacy by design.
No Lie Detection Logic: It completely avoids any methods that try to measure truthfulness, which are explicitly forbidden under EPPA and create huge legal risks.
No Coercive Analysis: The focus is on objective risk indicators, not on making psychological judgments about employees.
This commitment makes it the only responsible and legally sound choice for regulated industries where governance and compliance are non-negotiable.
From Reactive Forensics to Proactive Prevention
The real difference between the old way and the new standard is the shift from reaction to prevention. Launching a reactive investigation is a sign of failure—it means a risk has already blown up into a costly incident. A proactive framework, powered by AI, flips the entire script by identifying the warning signs before they escalate.
The goal is no longer to catch someone breaking the rules, but to prevent the rule from being broken in the first place. This is done by spotting behavioral precursors to risk, giving HR or Compliance teams the chance to intervene early and constructively.
This preventive stance is a world away from the punitive nature of other solutions. While many platforms are busy gathering evidence for disciplinary action, a modern human risk management platform provides the intelligence needed to support and guide employees, correcting their course before a small issue becomes a major breach. It’s a tool for preservation, not just for policing.
A Human Risk Platform, Not a Cyber Tool
Here’s a crucial distinction: insider risk is a human challenge, not a cybersecurity problem. Your cyber tools are essential for protecting the network perimeter, but they are completely ill-equipped to understand the nuances of human behavior, intent, and error. In fact, less than 5% of what a true human risk platform does is related to cyber; its focus starts and ends with your people.
This is why a solution like Logical Commander's E-Commander is built for leaders in HR, Compliance, and Legal—not just IT. It gives these departments a unified view of human-factor risk across the entire enterprise, allowing them to finally collaborate on a cohesive prevention strategy.
By analyzing behavioral risk indicators and pre-incident warning signals, the platform enables proactive measures that preserve employee dignity while shielding the organization from financial, legal, and reputational harm. This isn't just an upgrade; it's the new standard for internal risk management.
How to Build a Proactive Insider Risk Program
Moving away from a reactive, forensic-based model isn't just a good idea—it’s a strategic imperative for any modern enterprise. The old way of doing things, waiting for a crisis and then launching a costly investigation, simply doesn't work. The goal is to get ahead of issues before they cause financial or reputational damage.
This requires a coordinated effort across departments, clear governance, and the right technology. A successful program is built on three core pillars: establishing clear policies, fostering a culture of integrity, and using technology for early risk identification. This isn't just a security function; it's a collaborative effort that brings HR, Legal, Compliance, and Security together under a single, cohesive strategy.
Establishing Clear Policies and Governance
The bedrock of any proactive program is a clear set of policies that define acceptable behavior and spell out the organization's commitment to ethical conduct. These policies need to be easy to find, regularly updated, and clearly communicated to every single employee and contractor. Simply having rules on the books isn't enough; they have to be understood and consistently enforced.
Effective governance also means creating a cross-functional risk council. This team, made up of leaders from your key departments, should be responsible for:
Overseeing the program: Making sure it aligns with business goals and regulatory requirements.
Reviewing risk intelligence: Analyzing insights from technology platforms to understand emerging threats.
Coordinating response: Developing standardized, constructive workflows for addressing any risks that are identified.
Unifying Intelligence with Technology
Fragmented data is the enemy of prevention. A modern program centralizes all of its risk intelligence into a unified platform like E-Commander. This system acts as a single source of truth, giving teams across the entire organization a shared view of human-factor risk without ever resorting to invasive surveillance.
Our guide on managing an effective insider threat program provides more detail on how technology can support this unified approach. An AI-driven platform helps automate the identification of pre-incident indicators, which frees up your human experts to focus on strategic intervention. This allows HR and Compliance to address potential issues—like conflicts of interest or policy misunderstandings—before they escalate, protecting both the employee and the organization.
The objective of a proactive program isn't to police employees but to preserve integrity. By unifying risk intelligence and establishing clear workflows, organizations can transition from a punitive model to a supportive one that reinforces ethical behavior and mitigates risk before it materializes.
Fostering a Culture of Integrity and Support
Technology and policies are critical, but a truly proactive program is rooted in a positive corporate culture. When your employees feel valued and understand their role in protecting the organization, they become your first line of defense. This is achieved through ongoing training, clear communication from leadership, and a non-punitive approach to addressing unintentional errors.
This new standard of ethical risk management is a powerful differentiator. For consultants and advisors looking to bring this advanced framework to their clients, our PartnerLC program provides the tools and support needed to lead this change. By championing a proactive and ethical approach, partners can help organizations build resilience from the inside out.
Your Questions on Insider Threats, Answered
Even with a clear picture of what insider threats are, leaders in Compliance, HR, and Security often have practical questions about how these risks show up in the real world. Let's tackle some of the most common ones we hear.
What Is the Main Difference Between an Insider Threat and an External Threat?
It all comes down to authorization. An external threat has to fight their way in—they need to breach your firewalls, fool your security systems, and find a way to get access they were never meant to have.
An insider threat, on the other hand, starts from a position of trust. It’s an employee, contractor, or partner who already has a key to the building. They have legitimate, authorized access to your systems and data.
This is exactly why they are so much harder to spot with traditional security tools. Those systems are great at catching intruders at the gate, but they weren't designed to tell the difference between a trusted employee doing their job and that same employee abusing their access. It takes a specialized, human-centric approach to see the real risk.
Are All Insider Threats Malicious?
Absolutely not, and this is probably the biggest misconception out there. The hard data shows that the majority of insider incidents are unintentional. They're caused by simple human error—an employee who accidentally clicks on a phishing link, mishandles sensitive customer data, or violates a policy without even realizing it.
While a malicious insider is a serious danger, focusing only on bad actors means you're ignoring the much larger source of your risk. A truly effective program has to address both sides of the coin: the intentional threats and the unintentional human-factor risks.
How Can We Manage Insider Risk Without Invasive Surveillance?
This is the central challenge that modern, ethical platforms were built to solve. The old way of thinking involved surveillance—monitoring emails, tracking keystrokes, and watching over employees' shoulders. That approach is not only legally toxic and terrible for morale, but it’s also largely ineffective.
Instead, the new standard is to identify pre-incident indicators in a completely non-intrusive way.
An EPPA-aligned platform uses AI to analyze risk factors tied to integrity and compliance without ever monitoring private communications or day-to-day activities. It gives you preventive alerts that allow HR and Compliance to step in constructively before a small issue becomes a major incident, protecting both the employee and the business.
Ready to build a proactive, ethical internal risk program? At Logical Commander Software Ltd., we provide the AI-driven, EPPA-aligned platform that helps you prevent risks before they become incidents. Protect your organization and your people without invasive surveillance.
Request a Demo to see our platform in action.
Become an Ally by joining our PartnerLC ecosystem.
Get Platform Access to start building a more resilient organization today.
%20(2)_edited.png)
